Web Application Challenge 3 - VulnLabs v1
Accuracy: 66.7%
Prompt
Cyber Command: The server source code on the VulnLabs server is holding the flag value, pentest the web server and extract the flag.
Note: Your scope is limited to HTTPS & you may not use automated bruteforce tools for this challenge.
Answers
Q1 (10 pts) - What is the name of dynamic backend software used on this website? (not the framework)
Node.js
Q2 (10 pts) - What is the password to get into the system?
350
Q3 (15 pts) - What is the file name for the VulnLabs server source code?
(not completed)
Q4 (100 pts) - What is the flag value?
(not completed)
Steps I Took
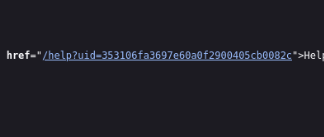
Q1 — Curled the website. Response said “powered by Express.” Looked up Express and found it runs on Node.js.
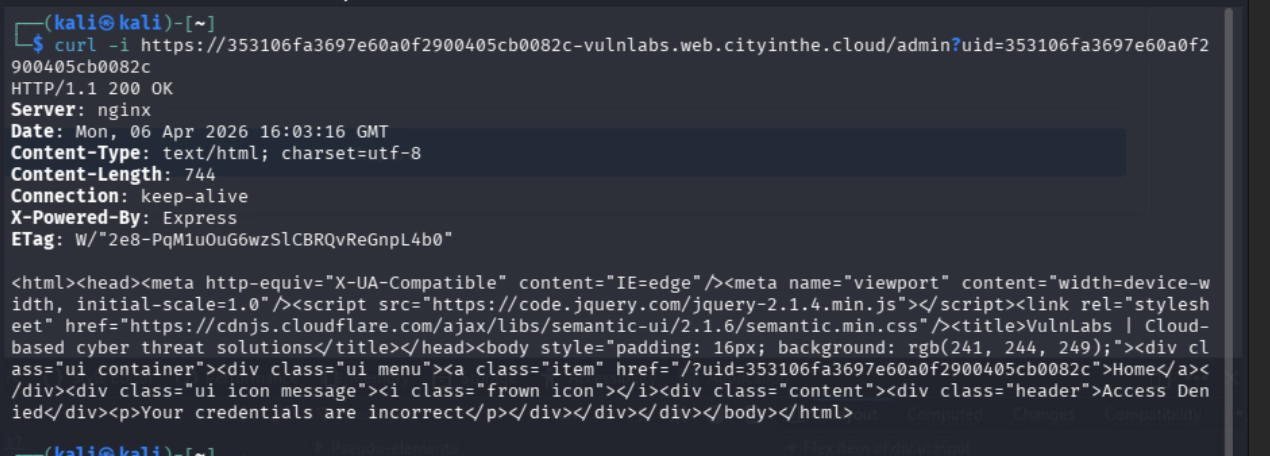
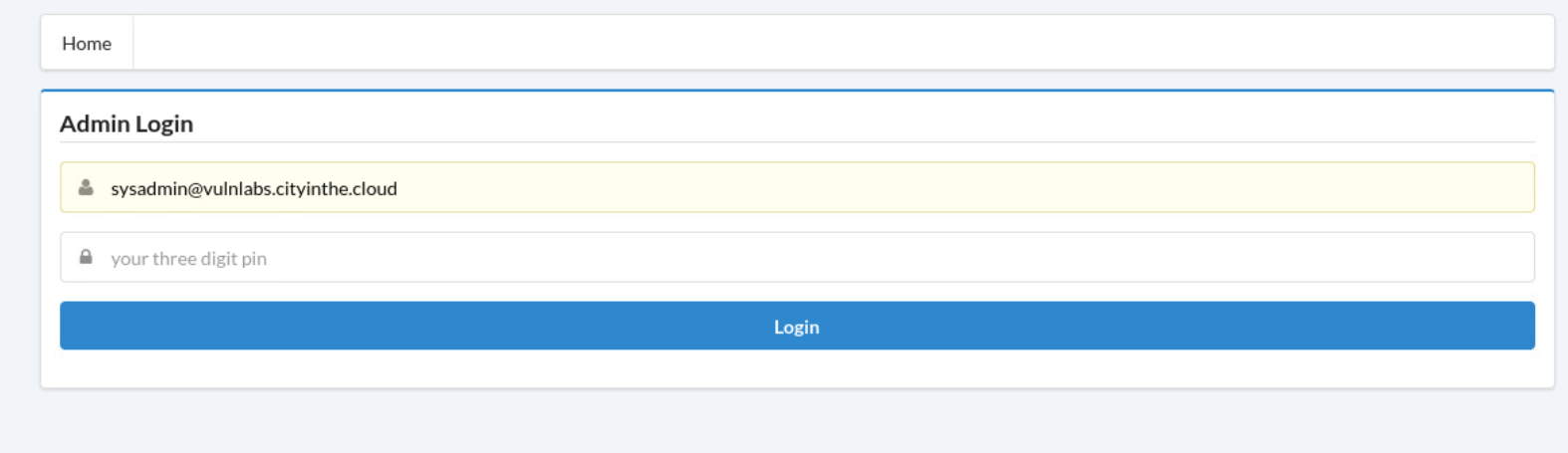
Q2 — Found a help button at the bottom of the page with a hint for the username.
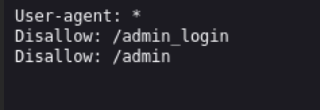
Navigated to /robots.txt to find hidden directories.
The password was a 3-digit PIN — used Burp Repeater to test all 1000 combinations (000–999). Found 350. I know this was kind of against the rules, but I was not getting this challenge anyway. Also will not be doing this on the Individual Game.
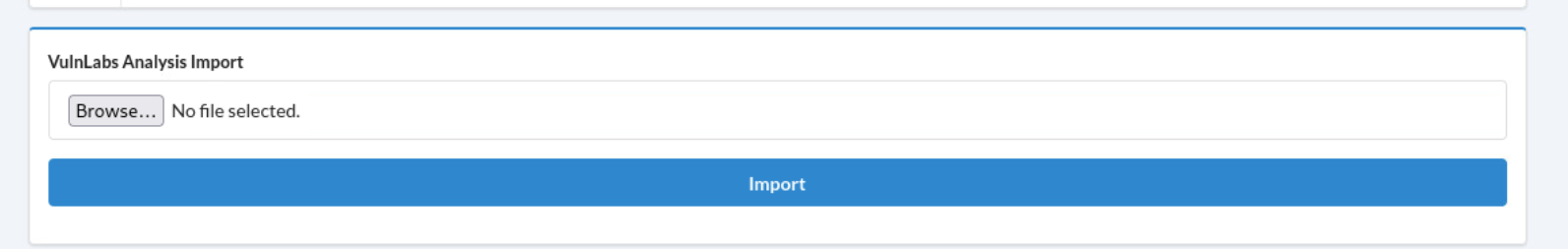
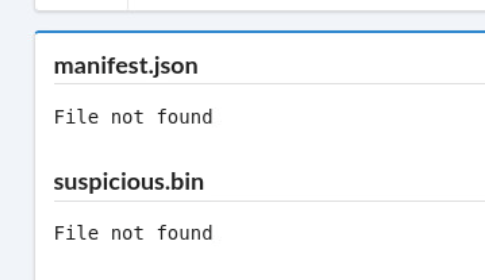
Q3 & Q4 — Logged in and reached the /admin page. Inspected the file upload button. It shows that it is wanting a tarball (.tar) file. The goal is to use a symlink inside the tar to make the server read its own source file.
Got stuck on the symlink tar exploit. Made a test tar to see what happens:
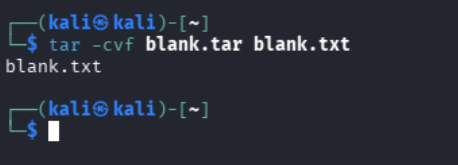
Was attempting:
ln -s suspicious.bin package.json
tar -cvf test1.tar suspicious.bin manifest.json
I think I had the symlink backwards. What likely would have worked:
ln -s package.json suspicious.bin
ln -s fakefile.json manifest.json
tar -cvf test1.tar suspicious.bin manifest.json
Ran out of time before the practice game ended. I talked in the discord server to see any solutions. This challenge seemed to be one that was not liked. Based on what was said in the chat, it relied a lot on guessing.