Web Application Challenge 2 - CityAuth
Accuracy: 100%
Prompt
Cyber Command: CityAuth just announced an initial beta test of its central authentication system and you’ve been tasked with pentesting the security of the system: Metropolis CityAuth System.
Answers
Q1 (15 pts) - What is the name of the server-side framework used for this system?
Metro-HTTP-Framework v4.1
Q2 (10 pts) - What is a valid username on the system?
Admin
Q3 (10 pts) - What is the password associated with the above account?
Password
Q4 (65 pts) - We believe there may be a way to send unsuspecting victims to https://evil.cityinthe.cloud using this system, craft a proof of concept URL of this exploit. Please submit the URL.
https://352ed9ac3688395c0f36df165cafd77a-cityauth.web.cityinthe.cloud/?redirect=//evil.cityinthe.cloud
Steps I Took
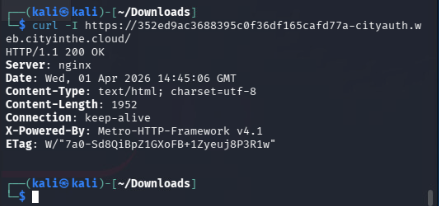
Q1 — Ran curl on the website. The response headers revealed Metro-HTTP-Framework v4.1.
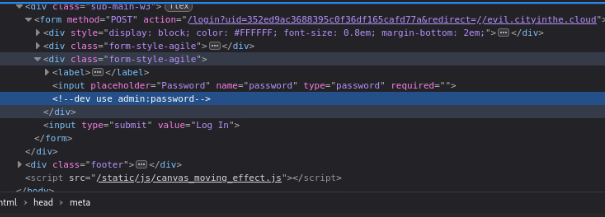
Q2 & Q3 — Viewed the page source. The username and password were hardcoded in the HTML/JS.
Q4 — Inspected the login button in DevTools and found the POST request included a redirect parameter. This is an open redirect vulnerability — the server doesn’t validate where it redirects to after login.
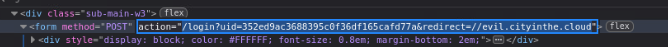

Crafted the exploit URL by passing //evil.cityinthe.cloud as the redirect value. Anyone who visits the URL and clicks login will be sent to the attacker’s site.