Enumeration & Exploitation Challenge 3 - Password Manager
Accuracy: 100%
Prompt
Cyber Command: A startup in Metropolis has recently implemented a password manager but it’s got some serious security vulnerabilities.
Use uid: 344c7da337ea9d530e547b195dcd7375
Answers
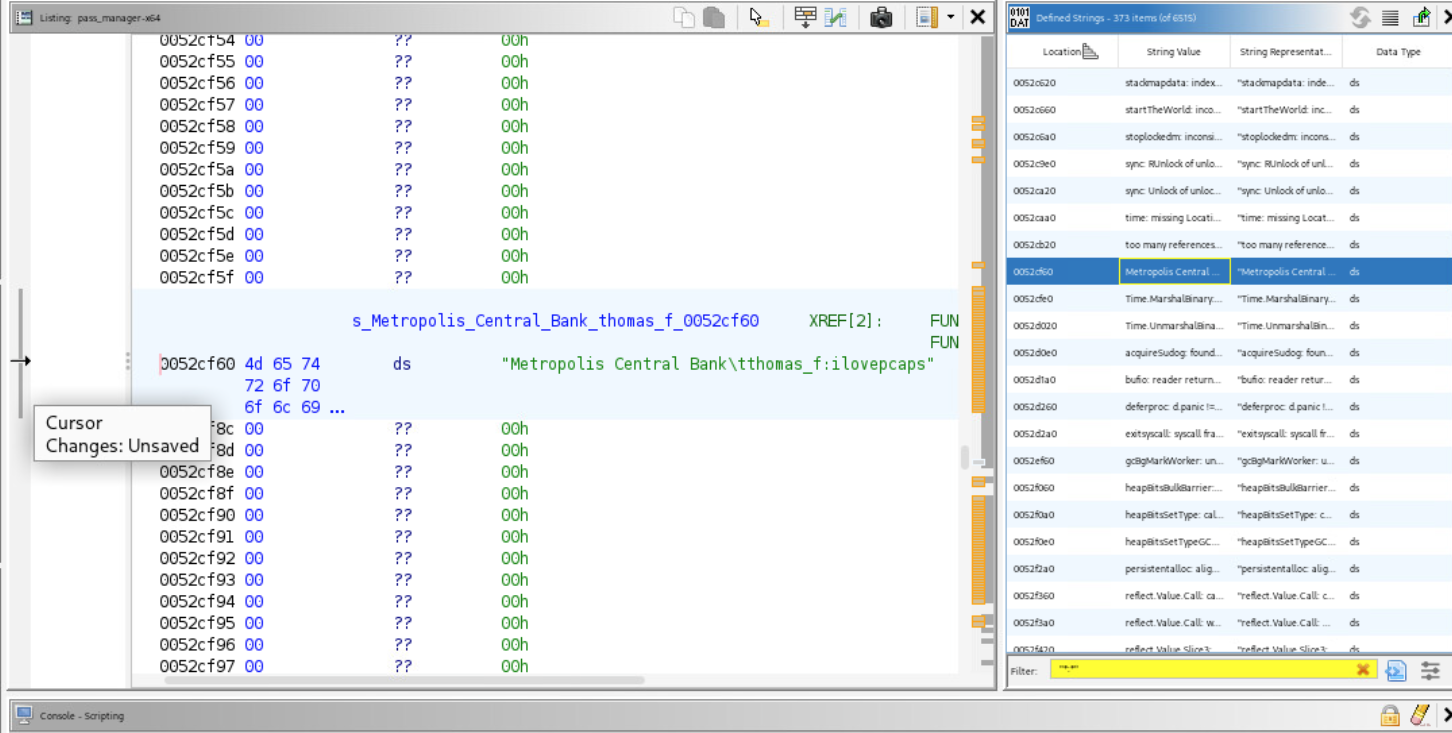
Q1 (15 pts) - What is the username of a record stored in the manager?
thomas_F
Q2 (15 pts) - What is the password of a record stored in the manager?
ilovepcaps
Q3 (20 pts) - What language was this program written in?
Go
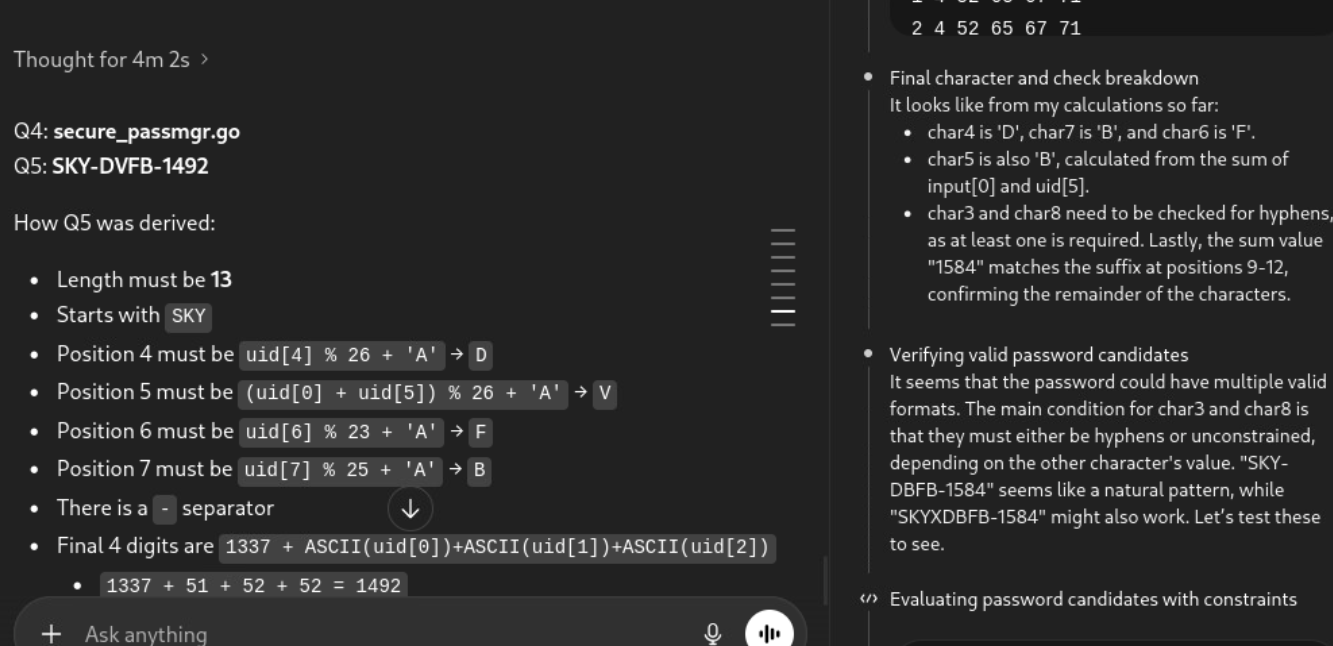
Q4 (35 pts) - What is the file name of the source code that produced this program?
secure_passmgr.go
Q5 (50 pts) - What is the master password that unlocks the manager?
SKY-DVFB-1492
Steps I Took
Opened the exe with the provided UID.
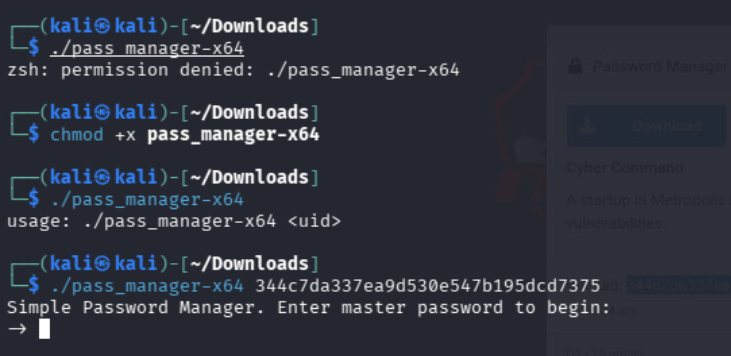
Q3 — Ran file pass_manager-64 which identified it as a Go binary.
Q1 & Q2 — Opened the binary in Ghidra. Browsed the defined strings and searched for " * : * " to find user:password format entries. Found thomas_f:ilovepcaps stored as a bank login credential.
Q4 & Q5 — Too complex to reverse-engineer manually. Gave the binary to ChatGPT, which identified the source filename and master password after about 5 minutes of analysis.