Password Cracking Challenge 5 - WiFi
Prompt
Cyber Command: This configuration file looks like it’s securing the password in a safe manner but we believe it could be cracked, can you find out what the passwords are?
network={
ssid="hotel-wifi"
psk=dacffc31a0db683b046249a1c521d7a3f6000e7c9633a64b50aa8cb2855aab18
}
network={
ssid="university-guest"
psk=9752f8bc198e546688025be9cb5dd95d61d52e904c8ef2d7babb0cc82376aeda
}
network={
ssid="corporate-iot"
psk=c50d6f76356494456c08709559a1a92667c9a40f211429da385b14dd4a42f5c2
}
Answers
Q1 (20 pts) - What is the hotel’s WiFi password?
hotel606
Q2 (20 pts) - What’s the university’s WiFi password?
college37
Q3 (20 pts) - What’s the corporate WiFi password?
Letmain07
Steps I Took
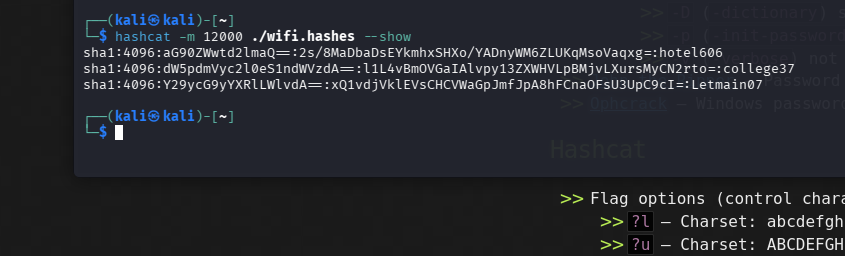
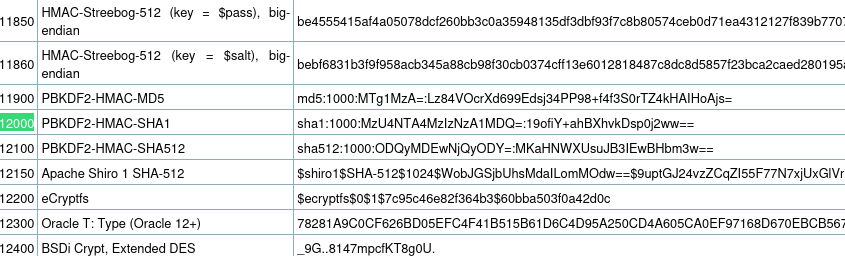
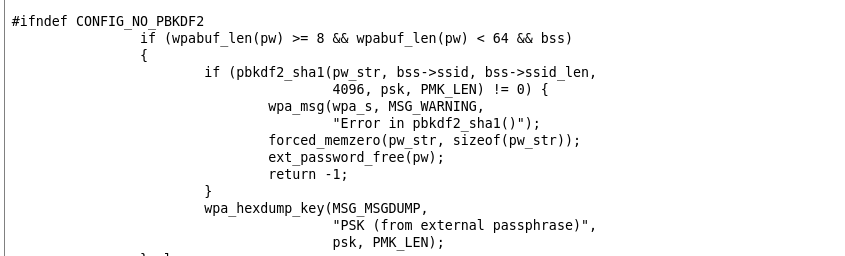
Searched “WPA2 PSK Hashes.” Found that these are PBKDF2-HMAC-SHA1 hashes (hashcat mode -m 12000). The SSID acts as the salt.
Needed to format hashes as: sha1:4096:base64(ssid):base64(psk_hex)
Used CyberChef to convert each SSID to Base64 (salt) and each PSK hex value to Base64 (hash):
sha1:4096:aG90ZWwtd2lmaQo=:2s/8MaDbaDsEYkmhxSHXo/YADnyWM6ZLUKqMsoVaqxg=
sha1:4096:dW5pdmVyc2l0eS1ndWVzdA=:l1L4vBmOVGaIAlvpy13ZXWHVLpBMjvLXursMyCN2rto=
sha1:4096:Y29ycG9yYXRlLWlvdA==:xQ1vdjVklEVsCHCVWaGpJmfJpA8hFCnaOFsU3UpC9cI=
Saved to a file and ran:
hashcat -m 12000 wifi.hashes /usr/share/wordlists/rockyou.txt