Forensics Challenge 3 - Unknown
Accuracy: 66.7%
Prompt
Cyber Command: We’ve obtained a drive that appears to hold some flags, but we can’t figure out how to extract them. Can you help?
Answers
Q1 (5 pts) - What filesystem is being used?
ZFS
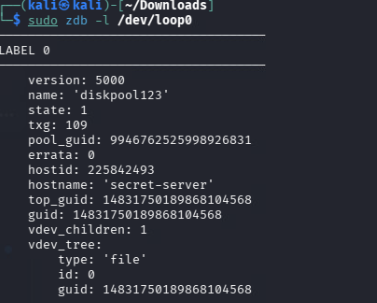
Q2 (10 pts) - What is the name of the pool used?
diskpool123
Q3 (10 pts) - What is the pool identifier?
9946762525998926831
Q4 (10 pts) - What is the disk space size? (shorthand)
(obtained, screenshot not saved)
Q5 (15 pts) - When was the pool last scrubbed? (rounded to nearest minute in UTC time)
2022-10-31 21:49
Q6 (15 pts) - What is the full name of the snapshot that is being protected from deletion?
diskpool123@jerry
Q7 (20 pts) - What is flag 1?
SKY-ZPOL-9257
Q8 (25 pts) - What is flag 2?
SKY-INVS-8302
Steps I Took
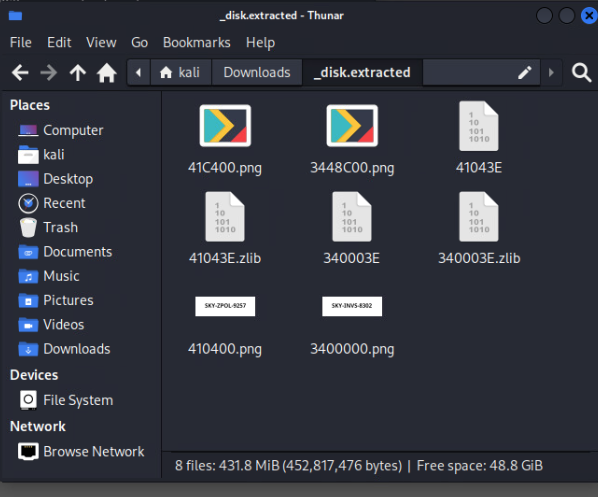
Downloaded disk.gz and extracted it. Ran binwalk on the disk image — it returned several extracted files, two of which contained the flags directly (Q7 and Q8).
Started with Volatility but realized it was the wrong tool — this is a disk image, not a memory dump.
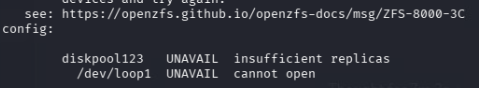
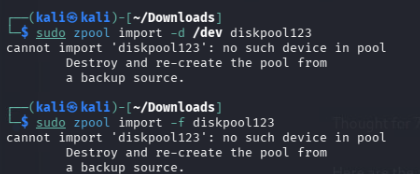
Switched to ZFS utilities. Had trouble getting it to mount at first, but restarted and retried.
For the UTC scrub time, the default output showed local time. Used:
sudo env TZ=UTC zpool status diskpool123
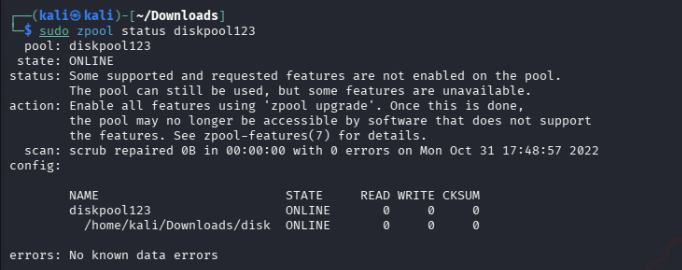
Got: 2022-10-31 21:49
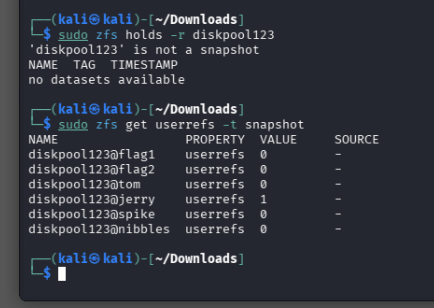
For the protected snapshot, ran a zfs holds command which confirmed diskpool123@jerry had a hold preventing deletion.